Apple Developer Stored XSS — $5,000 Bug Bounty Write-up
This article is a structured summary and rewrite based on a public security write-up regarding a Stored Cross-Site Scripting (Stored XSS) vulnerability that affected multiple Apple domains, including highly sensitive assets such as developer.apple.com.
The purpose of this write-up is to present the findings in a clearer, more organized format for educational and reference purposes within the security community.
All technical details, analysis, and timeline are derived from the original disclosure, which demonstrates how the issue was identified, validated, and ultimately remediated in collaboration with Apple Security.
This summary aims to help security researchers better understand the nature of the vulnerability and the importance of secure input handling in large-scale web applications.
Summary
During a security assessment of Apple Discussions and related Apple web properties, I discovered a Stored XSS vulnerability that allowed arbitrary JavaScript execution across multiple Apple domains.
The issue was initially found on discussions.apple.com, and later a bypass reintroduced the vulnerability across multiple Apple services.
Affected Domains
- discussions.apple.com
- developer.apple.com
- discussions-jp-prz.apple.com
- discussions-cn-prz.apple.com
- discussionskorea.apple.com
- discussionsjapan.apple.com
- discussionschinese.apple.com
- communities.apple.com
This indicates a shared backend architecture across multiple Apple discussion platforms.
Vulnerability Type
Stored Cross-Site Scripting (Stored XSS)
Severity: High
Attack Vector
User input inside forum posts was not properly sanitized, allowing HTML injection and JavaScript execution.
Steps to Reproduce
- Login to discussions.apple.com
- Go to “Ask the Community”
- Create a new thread or comment
- Inject payload (redacted)
- Submit post
- Open thread
- JavaScript executes automatically
Technical Details
The initial sanitization layer was bypassed using an alternate execution path, allowing payloads to be stored and executed server-side.
The payload executed automatically without user interaction, including on developer.apple.com/forums.

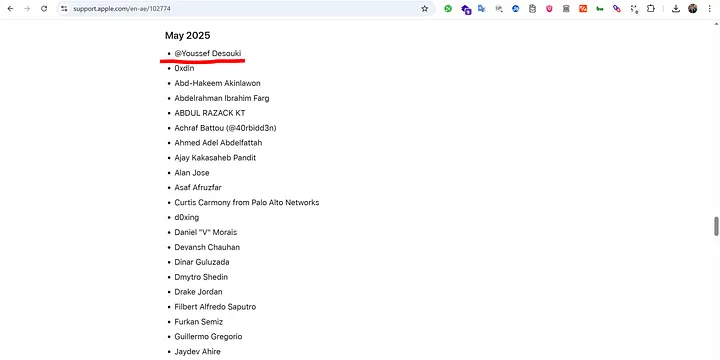
Apple Security Acknowledgement
Official response: Apple Security Advisory
Timeline
- March 31, 2025 — Initial report submitted
- April 5, 2025 — Apple confirms issue
- April 8, 2025 — Bypass discovered
- May 13, 2025 — Full fix deployed
- May 29, 2025 — Bounty approved
- July 31, 2025 — $5,000 payment issued
This case escalated from a simple Stored XSS into a multi-domain vulnerability affecting Apple’s global infrastructure.
Through responsible disclosure and collaboration with Apple Security, the issue was fully resolved.
The most valuable takeaway is that even small input fields can introduce high-impact security risks when deployed at scale.
Source
https://medium.com/@ZombieHack/apple-developer-stored-xss-5-000-bounty-writeup-2025-cc34a030a5bf





